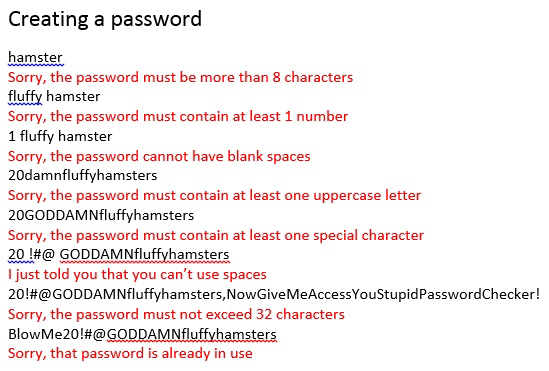
Obligatory https://neal.fun/password-game/
Programmer Humor
Post funny things about programming here! (Or just rant about your favourite programming language.)
Rules:
- Posts must be relevant to programming, programmers, or computer science.
- No NSFW content.
- Jokes must be in good taste. No hate speech, bigotry, etc.
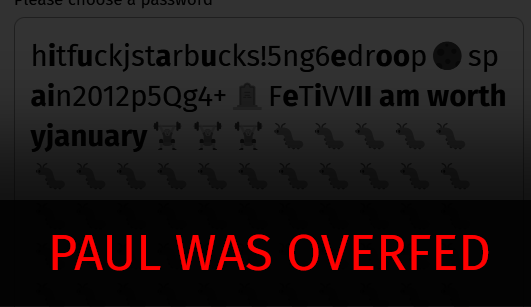
Well, that'll teach you to actually take care of your pets and not just dump their food in front of them and be done with it.
(fuck paul tho fr)
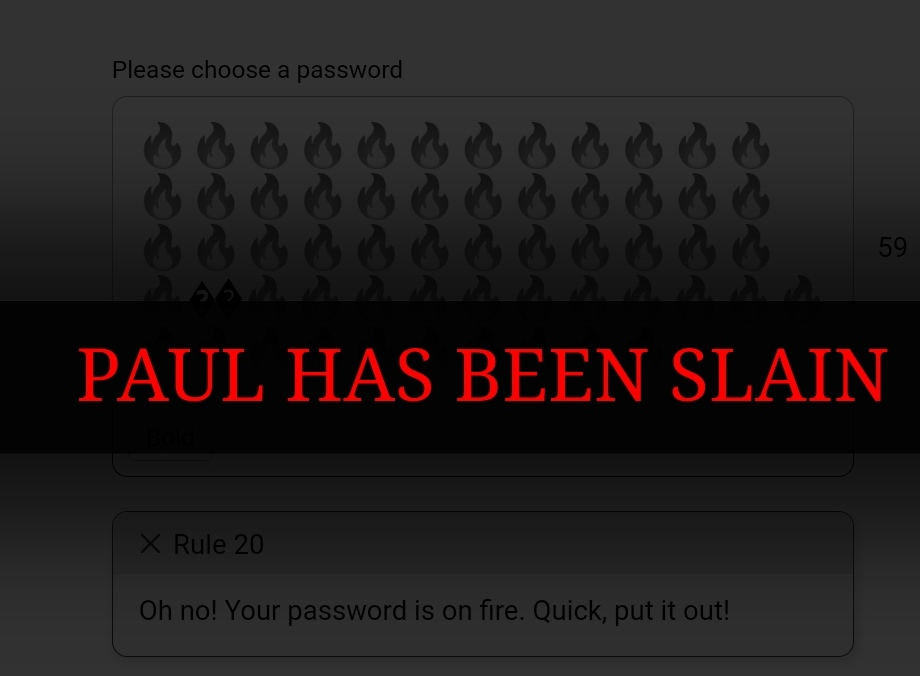
Nooo! The fireeee! This would be better with a physical keyboard.
 Link for compatibility
Link for compatibility
My final password was: Pass5@JulyXXXV+Shell+n2by7+droop+🌚+Peru+2020+Qd7+🥚+Zn+BBBBB
The hardest 2 were chess and guessing the country. Maybe atomic numbers with combination with roman numerals, but that's sorta fine.
Ah I was just copying the URL to post the same thing. It's such a fun game to go through, although I gave up pretty quickly
Tried it again, made it to the chess step
One of my coworkers got super into it and got into the high 20s I made an off-hand comment about wondering what it does for rule 34 and he responded "gasp I must know!" Then a couple days later messages me a screenshot on teams. Spoiler: it goes "ehhh let's just skip this rule"
Use lichess.org’s board editor
You're telling me I didn't need to use my brain?
You're on programmer humor, we don't do "Brain" here.
This game made me so angry haha
Infuriating fact: if a service has maximum password length limits (lower than 1000 characters), they're reversibly storing your password and if they're that lazy it's probably plain text
reversibly?
Yeah, you actually better not save the users passwords in plain text or in an encrypted way it could be decrypted. You rather save a (salted) hashed string of the password. When a user logs in you compare the hashed value of the password the user typed in against the hashed value in your database.
What is hashed? Think of it like a crossfoot of a number:
Let's say you have a number 69: It's crossfoot is (6+9) 15. But if someone steals this crossfoot they can't know the original number it's coming from. It could be 78 or 87.
Dumb question: isn't it irrelevant for the malicous party if it's 78 or 87 per your example, because the login only checks the hash anyway? Won't both numbers succesfully login?
It's actually a really good question. What you're explaining is called a collision, by creating the same hash with different numbers you can succesfully login.
This why some standard hashing function become deprecated and are replaced when someone finds a collision. MD5, which was used a lot to hash passwords or files, is considered insecure because of all the collisions people could find.
In the example yes.
In the real world, finding an input that produces the right hash output isn't easy. And because a lot of users reuse passwords (don't do it, but people do), a list of emails and passwords gives you an incredibly lazy and easy to do way to compromise accounts on other sites.
Reminds me of a funny moment in my IT internship, ahead of an audit one of the sysadmins came over and was saying "yeah so I pulled all of the department password hashes to check for weak/compromised accounts and noticed one person has the same sysadmin and user password hash" and my boss went "wait everyone doesn't do that?" And after realizing they outed themselves turned bright red and changed their admin password
With a hash it's difficult to find a combination that results in this specific hashed password. Think of it like this: you have a biiig prime number and you multiply it by another. Now, that's easy, but it's way harder to do it backwards - factorize a large composite number (this is just for illustration). Similarly trying to find a password that works when you input it based on the hashed one is way more difficult than hashing the password in the first place.
Additional to what others have said: The "salted" part is very relevant for storing.
There aren't soooo many different hashing algorithms people use. So, let's simplify the hashing again with the crossfoot example.
Let's say, 60% of websites use this one algorithm (crossfoot) for storing your password, and someone steals the password "hashes" (and the login / email). I could ran a program that creates me a list of all possible crossfoots for all numbers for 1 to 100000.
This would give me an easy lookup table for finding the "real" number behind those hashes. (Those tables exists. Look up "rainbow tables")
Buuuut what if I use a little bit of salt (and pepper pepper pepper) before doing my hashing / crossfooting?
Let's use the pw "69" again and use a salt with a random number "420" and add them all together:
6 + 9 + 420 = 435
This hash wouldn't be in my previous mentioned lookup table. Use different salts for every user and at least the lookup problem isn't such a big problem anymore.
This was super helpful 🙏🏼 sent me down a whole other rabbit hole of learning
In the least bad case, they encrypt the password instead of hashing it, making it possible to decrypt the password.
In the most common case, they store the password in plaintext, so there isn't even any encryption to be reversed.
Best practice in 2023 is a simple, sufficiently long but memorable passphrase. Excessive requirements mean users just create weak passwords with patterns.
[Capital letter]basic word(number){special character}
Enforcing password changes doesnt help either. It just creates further patterns. The vast majority of compromised credentials are used immediately or within a short time frame anyway. Changing the password 2 months later isnt going to help and passwords like July2023!, which are common, are weak to begin with.
A non expiring, long, easily remembered passphase like
forgetting-spaghetti-toad-box
Is much more secure than a short password with enforced complexity requirements.
Drop "memorable". 99.9% of your passwords should be managed by your password manager and don't need to be memorized. On one or two passwords that you actually need to type (like your computer login) need to be memorable.
99.9% of your passwords should be managed by your password manager
this looks like a sensible approach until you remember password managers can be cracked, too. I'm with GP on this, a passphrase is easier to remember and is good enough for most use cases, if you need more security you should be using some form or another of 2FA anyway
I don't get why some sites limit your usage of special characters and have miniscule max lengths?? looking at you PayPal you piece of shit
"This password would take 1 century to crack!"
There was a website where I was making an account and it was like: no semicolons.
To this day I wonder if that was how they blocked sql injection.
Then, please give us your phone number for 2fa, instead of letting you use a more secure app
The right answer is use a password manager to generate and store a long password. Then it doesn't matter.
If for some reason you want a secure password and aren't using a password manager https://www.grc.com/passwords.htm
Does anyone use the generator from chrome anymore? Like a 2023 password for me is "suggest strong password"...
"password must contain a PUA codepoint"